The website uses cookies to deliver services in accordance with the Cookies Policy. You can define the conditions for storing or accessing the cookie mechanism in your browser.

ThreatDown Managed Threat Hunting
SOLUTION OVERVIEW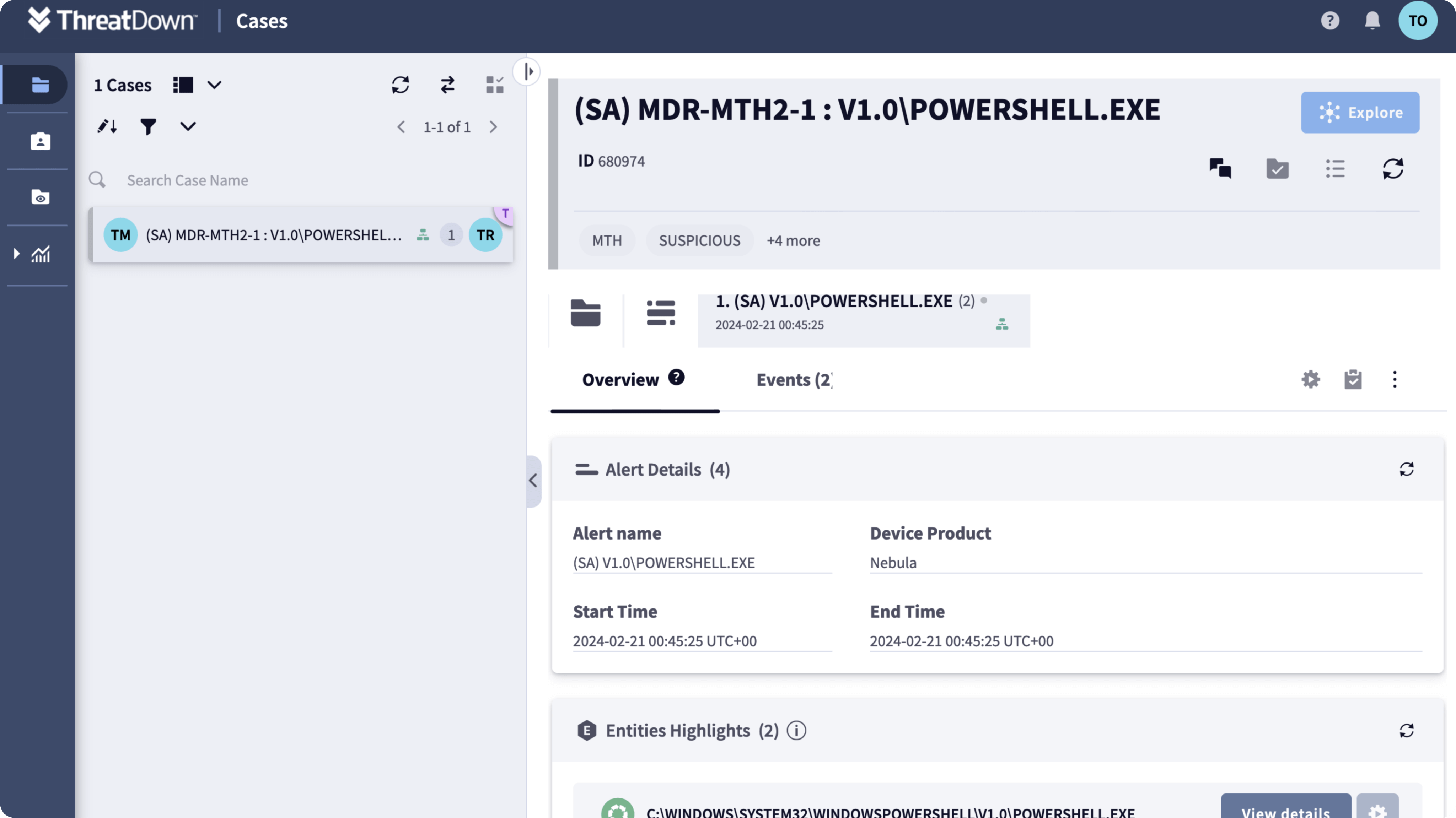
Empower your threat response with 24x7x365 service for alert prioritization and guided remediation with ThreatDown Managed Threat Hunting.
Organizations that monitor their own endpoints often suffer from an overwhelming number of endpoint security alerts. Combined with a lack of expertise in recognizing advanced and emerging indicators of security breaches, the result is many alerts that are ignored, leading to missed threats and potentially dire security and financial consequences. The longer intruders stay on networks and endpoints, the more time they have to gather information and execute a plan to harm the company. ThreatDown Managed Threat Hunting is a 24x7x365 service that proactively identifies and prioritizes critical alerts. Using internal and external threat analysis, MTH discovers events, behaviors and threats that may be unknown, hidden or overlooked. When a threat is detected, MTH notifies you of the details and sends you an easy to follow, set of remediation steps. This information enables IT staff to prioritize and fix incidents before the problem escalates.
FEATURES
24x7x365 Threat Hunters: Identify indicators of compromise using internal and external threat intelligence, bolstered by our many years of experience. Our accomplished Threat Hunters are always working even when you’re not.
Risk Mitigation: Finds hidden intruders faster as well as reducing dwell time and potential for damage to significantly reduce the risk of a crippling breach.
Alert Prioritization: Cuts through the noise to identify critical alerts that require immediate attention, giving you more control, stronger security, and greater confidence
Guided Response : Notifies customers with step-by-step guidance for easier and faster remediation resulting in time and cost savings.
EDR Integration: MTH is built to optimize the usage of internal and external intelligence in combination with the alerts gathered by ThreatDown Endpoint Detection & Response Integration.
How Does it Work?
On a recurring basis (both weekly and adhoc), MTH creates a unique dataset within the SOAR system that includes endpoint security alerts enriched with external threat intelligence. MTH creates and deploys a hunt strategy (e.g., search, analytics) for each threat hunt. Hunting strategies may include searching for evidence in the early or late stages of an intrusion that follows MITRE’s seven stage ATT&CK lifecycle. For example, a search may focus on IOC in the internal reconnaissance or lateral movement stages. Recent threat intelligence may form new hypotheses which will be used to influence the hunt strategy for a particular session. Once the search is executed and discovers IOC that match the hunt criteria; a notification, including a link to the EDR alert, is sent to the customer along with guided remediation content specific to the detected IOC detected. The customers follows the step-by-step instructions to address the IoC.
IT solutions

Test a product
On local martkets Bakotech Group operates through a well-established partner network, including over 1,000 active dealers. Key IT-integrators and are involved in the realization of large-scale projects concerning implementing solutions for end-customers from various segments of business. Bakotech's business strategy is True Value Added Distribution or in other words - project oriented distribution.
We are providing our partners with a wide range of services such as PR, co-marketing activities, pre post-sales support, trainings for partners and end-customers, PoC, PoV, solution consulting, implementation support and technical support.
Contact Us
Bakotech Sp. z o.o.
Dane firmy
VAT ID 6762466740
REGON 122894922
KRS 0000467615
Kontakt
ph. +48 12 340 90 30












